- 7.6.1.
defaultAuthPlugin - 7.6.2.
user.mapFile Format - 7.6.3. Dual-Paswords and MySQL 8
- 7.6.4.
user.mapDirect Routing - 7.6.5.
user.mapHost Options - 7.6.6.
user.mapUpdates - 7.6.7. Generating
user.mapEntries from a Script - 7.6.8. Encrypting
user.mapData - 7.6.9. Synchronizing
user.mapData - 7.6.10.
user.mapLimitations - 7.6.11. Host-based Authentication
When configuring Tungsten Connector it is important to ensure that you have
a user.map in place. The role of
user.map is to define the usernames and passwords of
users that will be connecting to the dataserver.
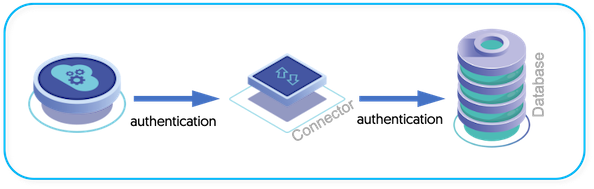
There is no authentication within the connector. Instead, the connector sends authentication information onto the dataserver. However, the MySQL network protocol exchanges a token between the client and the dataserver in order to authenticate the connection and is designed to prevent 'man in the middle' attacks.
Unfortunately, 'man in the middle' is exactly how Tungsten Connector
operates, as the man in the middle to redirect queries to different
dataservers as the list of active dataservers changes during the operation
of a cluster. The authentication exchange cannot be reinitiated by the
dataserver and client, so the Tungsten Connector performs this
authentication exchange on behalf of the client using the user and
password information from a special file called
user.map.
To get round this limitation, the connector operates as follows:
Client opens a connection to the connector and authenticates.
Connector connects to the datasource using the username supplied by the client, and the corresponding password stored within
user.map.Database server returns the authentication token to the connector.
Connectors sends the same authentication token back to the client.
This process gives the client application the authentication token required to enable it to communicate with the dataserver and the same token to be used by the connector.
For this system to work, a file, user.map, must exist
on every connector installation, and it must contain the information for
all users that will connect to the datasources from each client. Without
this information, connectors will be unable to login on behalf of the
client applications.
Important
All the users that require access to your MySQL servers through the
Tungsten Connector must have an entry in the
user.map. Without this information, the
Tungsten Connector has no way of providing an onward connection to a MySQL
server.
The user.map file primary role is to operate as the
source for authentication information within the connector. However,
through the use of additional flags and keywords, the file can also define
the routing methods used by different users when connecting to
datasources, and different dataservices.
By default, Tungsten Connector mirrors the default authentication plugin used by the MySQL backend:
mysql_native_passwordfor versions up to and including MySQL 7.xcaching_sha2_passwordfor 8.0 and above
It is possible to overide the default by specifying the tpm flag
property=defaultAuthPlugin=<caching_sha2_password|mysql_native_password>
within your /etc/tungsten/tungsten.ini